Why General-Purpose AI Agents Fail AIFMD Compliance
🇩🇪 Auch auf Deutsch verfügbar- OpenClaw has 7+ CVEs in its first two months, including a CVSS 8.8 one-click RCE.
- 42,900 exposed instances found across 82 countries with leaked API keys.
- NVIDIA's NemoClaw adds sandboxing but addresses zero AIFMD-specific requirements.
- AIFMD compliance requires tenant isolation, filing state machines, XSD validation, NCA protocols, and immutable audit trails — none of which exist in any general-purpose agent framework.
- Building "AIFMD tools" on top of OpenClaw replaces it. The domain logic is the product.
The rise of autonomous AI agents — led by OpenClaw's explosive growth to 250,000+ GitHub stars — has prompted fund managers and compliance teams to ask a reasonable question: can we use a general-purpose AI agent for AIFMD regulatory reporting?
The short answer is no. Not today, and not without fundamental architectural changes that defeat the purpose of using a general-purpose framework. This paper explains why.
1. The Security Problem Is Not Theoretical
OpenClaw's security track record is disqualifying for regulated finance.
OpenClaw's Control UI trusts a gatewayUrl parameter from the query string and automatically establishes a WebSocket connection without user confirmation, transmitting authentication credentials to the attacker-controlled server. A single malicious link gives the attacker operator-level access to the agent gateway, enabling arbitrary configuration changes and remote code execution on the host.
Affected: all versions before 2026.1.29 · CWE-669 (Incorrect Resource Transfer Between Spheres)
Six Additional Vulnerabilities
Researchers subsequently disclosed six more vulnerabilities including server-side request forgery (SSRF), missing authentication on API endpoints, and path traversal bugs — ranging from moderate to high severity.
42,900 Exposed Instances
Between January and February 2026, security firms identified over 42,900 public-facing OpenClaw instances across 82 countries. Many were running with default configurations, exposing API keys, environment variables, and database credentials to prompt injection attacks.
Regulatory Response
China's Ministry of Industry and Information Technology issued formal warnings. South Korean tech companies banned OpenClaw internally. Cisco's security team called it "a security nightmare."
For any fund manager subject to AIFMD, deploying a system with this security profile for regulatory reporting is a compliance violation in itself. Article 18 of AIFMD II requires AIFMs to maintain operational risk management systems that are "proportionate to the complexity of the business." Running a system with known RCE vulnerabilities against production fund data fails this test on its face.
2. AIFMD Requires Domain-Specific Controls, Not Generic Guardrails
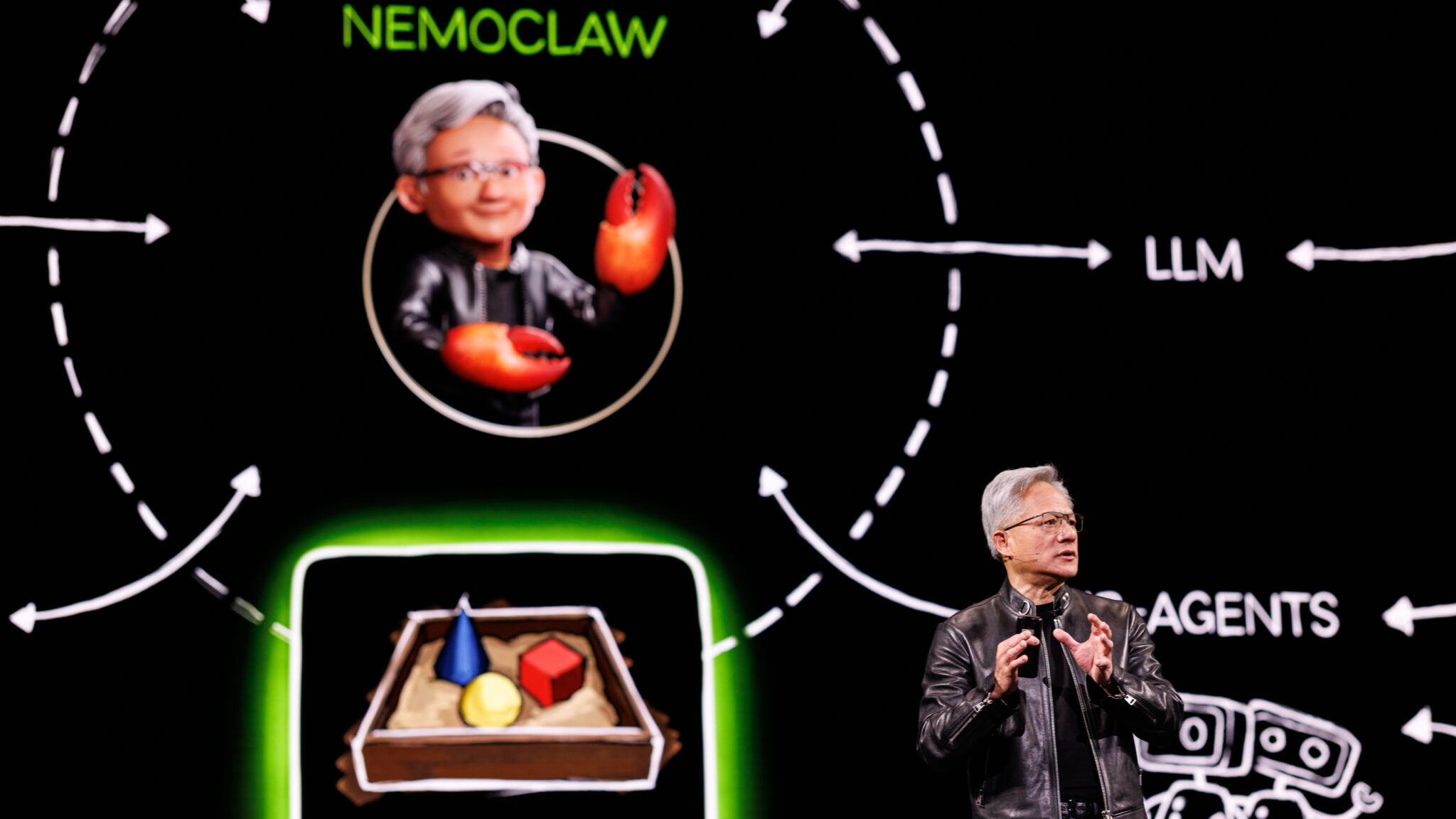
At GTC on March 16, Jensen Huang unveiled NemoClaw with a simple pitch: "It finds OpenClaw, downloads it, builds you an AI agent." He called OpenClaw "definitely the next ChatGPT."
NVIDIA's NemoClaw is an open-source security layer for OpenClaw, the autonomous AI agent framework created by Austrian developer Peter Steinberger and now governed by an independent 501(c)(3) foundation. NemoClaw is a MIT-licensed TypeScript plugin that installs into OpenClaw via openclaw.plugin.json. It extends OpenClaw; it does not replace it. The underlying agent runtime, tool execution model, and data handling remain OpenClaw's responsibility. (Source: github.com/NVIDIA/OpenShell)
NemoClaw exists in large part because OpenClaw shipped with serious security gaps (see Section 1 above). The enterprise sandboxing, policy-based guardrails, and privacy routing it adds are technically impressive — and completely insufficient for AIFMD compliance.
What NemoClaw Provides
| Control | Description |
|---|---|
| OpenShell sandbox | 4-layer kernel isolation: Landlock filesystem restrictions, seccomp syscall filtering, network namespaces, container-level process isolation |
| Privacy router | Intercepts outbound inference calls; routes through approved backends (NVIDIA cloud, local NIM, local vLLM) |
| Operator approval gates | Novel outbound network requests surfaced in text UI for operator approval. Note: these are infrastructure approvals ("allow api.openai.com?"), not domain-specific regulatory approvals |
| Declarative policies | Version-controlled, auditable network/filesystem/process rules; hot-reloadable at runtime |
| Nemotron models | Auto-evaluates local hardware; deploys Nemotron locally when GPU resources are sufficient |
Platform constraints: NemoClaw requires Ubuntu 22.04+, Docker, and a fresh OpenClaw installation. No Windows Server or RHEL support. No automatic model failover — if the configured model goes down, the agent stops entirely. Alpha-stage software with documented instability.
What AIFMD Actually Requires
| Requirement | AIFMD Article | What It Means for AI Agents |
|---|---|---|
| Tenant isolation | Art. 8 | Every database query, every API call, every audit log entry must be scoped to a single AIFM. Cross-tenant data leakage is a supervisory breach. |
| Immutable audit trail | Art. 46 | Every action the agent takes must be logged with timestamp, user, tenant, and full input/output. Records retained 5+ years. |
| Filing state machine | Art. 24 | Annex IV filings follow a strict lifecycle: draft → validated → submitted → acknowledged. No skipping steps. Each transition auditable. |
| Optimistic locking | Art. 18 | Concurrent access to filing records must not corrupt data. Requires application-layer locking. |
| NCA-specific protocols | Art. 24 + NCA | BaFin: WS-Security SOAP. FCA: Gabriel. AMF: Geco. Each NCA has different submission formats and auth mechanisms. |
| XSD validation | ESMA technical standards | Annex IV XML must validate against AIFMD_DATAIF_V1.2.xsd before submission. Invalid XML triggers supervisory questions. |
| Data sovereignty | GDPR + national | Investor PII must not leave the jurisdiction without GDPR Art. 46 transfer mechanisms. |
NemoClaw's sandboxing — even with four kernel-level isolation layers — does not address a single one of these requirements. Landlock can restrict filesystem paths; it cannot enforce that every SQL query includes a tenant_id filter. The privacy router can intercept inference calls; it cannot validate that Annex IV XML conforms to ESMA's AIFMD_DATAIF_V1.2.xsd schema. Seccomp can block dangerous syscalls; it cannot implement the filing state machine required by Article 24. NemoClaw's operator approval gates ask "should the agent call this URL?" — not "should this filing be submitted to BaFin?" You can't seccomp your way to compliance.
3. The "Compliance Claw" Fallacy
Some argue that OpenClaw's extensibility means a team could build an "AIFMD compliance claw" — a set of tools and prompts on top of the agent framework. This argument underestimates the depth of domain knowledge required:
- 14+ specialized tools — not "query database" and "search web," but
generate_annex_iv,validate_annex_iv_xml,check_eligibility,transition_filing,screen_investor,check_deadlines— each with AIFMD-specific business logic. - Database schema awareness — the agent must understand relationships between fund structures, investors, holdings, filings, delegation arrangements, and liquidity management tools. PE/VC closed-ended funds use committed capital as AUM basis. Multi-currency calculations must convert to EUR.
- Confirmation gates — creating a filing or transitioning to "submitted" are irreversible regulatory actions. The agent must pause and require human approval. General-purpose frameworks have no concept of action-level confirmation gates.
- PII handling — investor names, tax IDs, and LEIs must be stripped before transit to cloud LLMs. This happens at the tool result level, not the network level, because the agent needs to reference investors in reasoning while protecting their identity in transit.
- SQL safety — read-only SELECT queries against a whitelist of allowed tables. No access to
users,refresh_tokens, orlogin_attempts. Every query must include atenant_idfilter anddeleted_at IS NULLfor soft-deleted tables.
Building all of this on top of OpenClaw doesn't leverage OpenClaw — it replaces it. The agent runtime becomes a thin shell around domain-specific code that could run anywhere.
4. What Purpose-Built AIFMD Compliance Looks Like
Caelith was designed from the ground up for AIFMD compliance. Every architectural decision reflects regulatory requirements, not retrofitted guardrails.
Tenant Isolation by Design
Every database query is scoped to a tenant. There is no code path that can access data across tenant boundaries. This is enforced at the query layer (queryWithTenant for positional parameters, queryInTenantContext for named parameters), not at the network layer.
Immutable Audit Trail
Every agent action is logged — tool calls, confirmation requests, confirmation responses, filing state transitions. Audit records include tenant ID, user ID, timestamp, action type, and full input/output payloads. The audit trail is queryable per session, per user, and per filing.
Filing State Machine
Filing submissions follow a strict lifecycle enforced at the application layer:
Each transition is validated. Skipping steps is not possible. The transition_filing tool requires explicit human confirmation. State transitions use optimistic locking to prevent concurrent corruption.
NCA-Specific Submission
Caelith implements NCA-specific submission protocols — including BaFin's WS-Security SOAP interface with dry-run mode for testing. The system supports 8 NCAs today: BaFin (DE) and CSSF (LU) automated, AT/FR/NL/IE/IT/ES manual XML upload.
XSD Validation
Every generated Annex IV XML document is validated against ESMA's official AIFMD_DATAIF_V1.2.xsd schema before it can be submitted. Validation errors are surfaced with specific field-level feedback.
Data Sovereignty Options
Caelith's LLM layer is provider-pluggable (Claude via Anthropic is the production default; other backends are on the roadmap). For clients who cannot send data to US-hosted cloud LLMs, local-LLM execution is on the product roadmap (not yet shipped); today, Caelith mitigates this by applying a PII-stripping layer to every outbound prompt and by routing to Anthropic (US) under GDPR Chapter V safeguards (EU-US DPF / SCCs) as documented in the DPA.
5. The Bottom Line
| Dimension | OpenClaw + NemoClaw | Caelith |
|---|---|---|
| Security posture | 7+ CVEs in 2 months, 42K+ exposed instances | Zero public CVEs, tenant-isolated from day one |
| AIFMD knowledge | None | Full Annex IV lifecycle, 8 NCAs, XSD validation |
| Audit trail | Generic logging | Comprehensive: per-tool, per-session, per-filing |
| Filing workflow | None | Enforced state machine with confirmation gates |
| Data sovereignty | NemoClaw privacy router (alpha) | Multi-provider backend, on-prem local model support |
| Production readiness | Alpha (NVIDIA's own description) | Production-ready, German BaFin pilot |
| Regulatory controls | Generic sandboxing | Tenant isolation, PII stripping, SQL whitelisting, optimistic locking |
| Model failover | None — agent stops if model goes down | Automatic fallback chain across 4 providers |
| Platform support | Ubuntu 22.04+ only, requires Docker | Any platform (Node.js), cloud or on-prem |
General-purpose AI agent frameworks are powerful tools for general-purpose tasks. AIFMD compliance is not a general-purpose task. It requires domain-specific controls that cannot be bolted on after the fact — they must be built into the foundation.
Caelith is a multi-tenant AIFMD compliance platform with an integrated AI agent for regulatory reporting, Annex IV generation, and NCA filing submission. Built in Germany. Designed for European fund managers.
See Purpose-Built Compliance in Action
Watch Caelith's AI agent generate an Annex IV report, validate it against ESMA's XSD, and file to BaFin — with a full audit trail. No OpenClaw required.
Book a Demo →